0day Exploit Database 🌴 on Twitter: "Do you want to buy or sell exploits? #1337day #Exploit #0day Market. green vs black style. http://t.co/Di2f0b8Qz9 http://t.co/pNKifjogn6" / Twitter
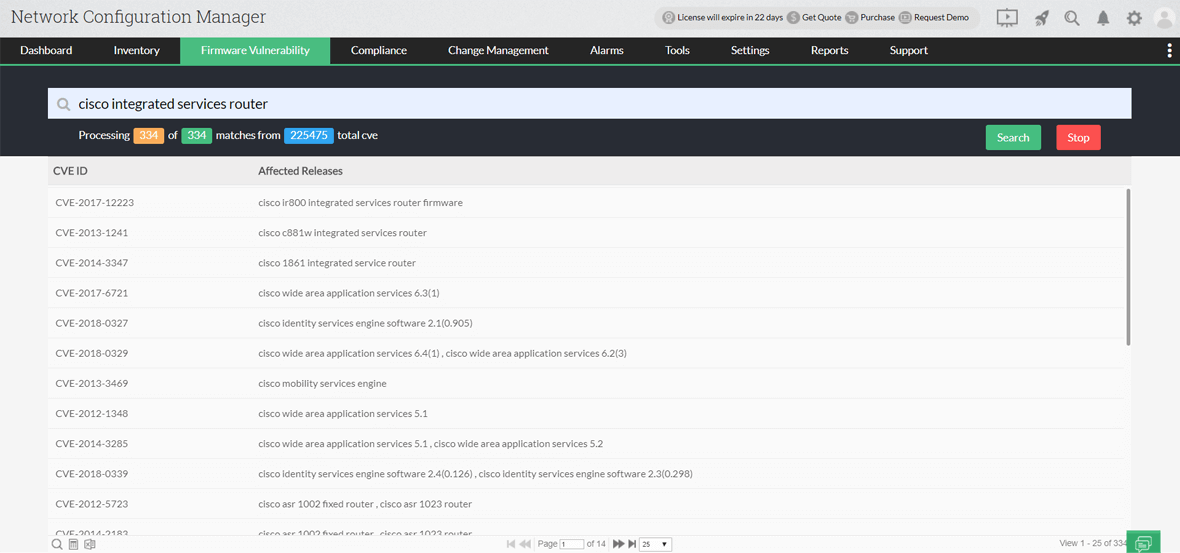
Firmware Vulnerability Management & NCM Vulnerabilities - ManageEngine Network Configuration Manager